The subject of user data is hotter than ever. We certainly don't want a stranger to get information about us. Therefore, it is important that we do not disclose certain information freely. However, there are some common privacy mistakes that can jeopardize the integrity of our data.
At Zemsania we are specialists in Digital Transformation and we believe that avoiding malpractice can save us a lot of trouble.
In most cases, it can take us days to realize that our data has been illegitimately obtained. However, breaking the security of a device takes no more than a few hours. That is why we must reinforce security by avoiding these bad practices.
The most recurrent privacy errors
Here are some of the most common privacy mistakes. Don't worry; we've all made at least one of these mistakes at one time or another. It's time to learn from the past and boost our data security.
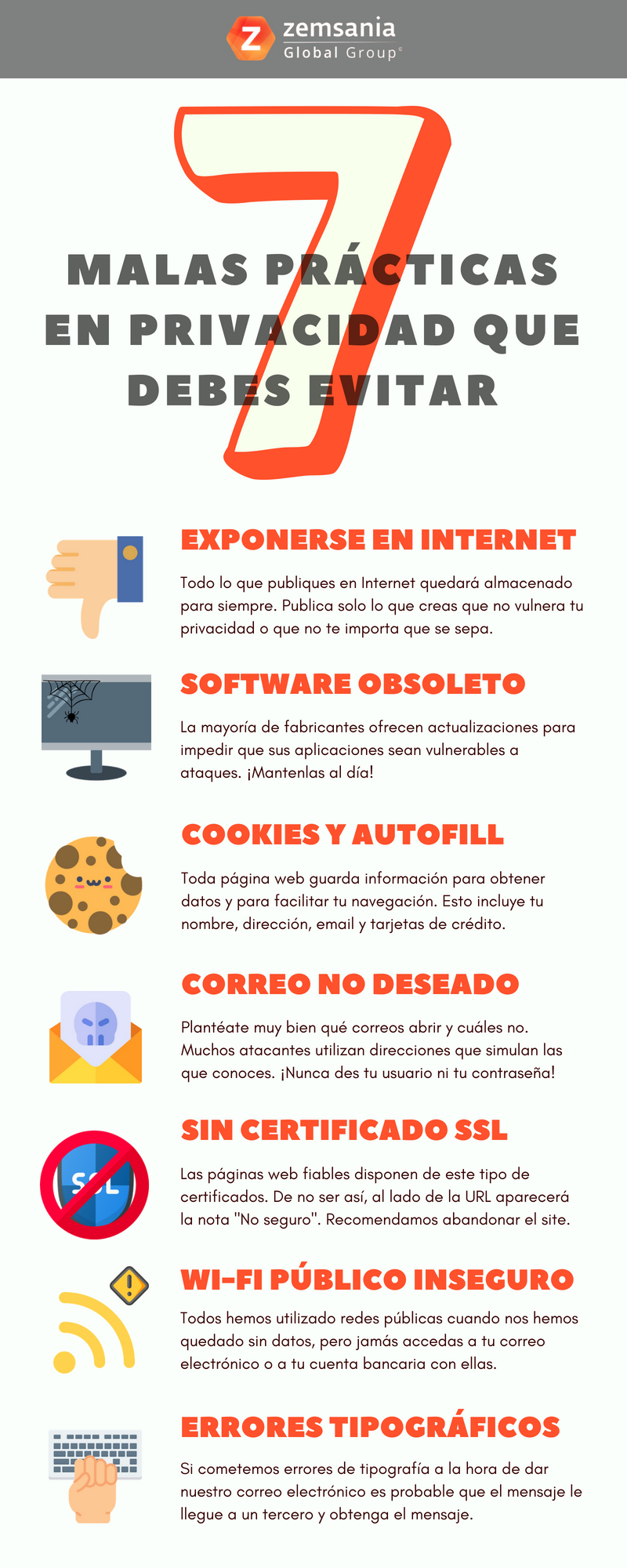
Publications in networks and Internet in general
What you post on the Internet stays on the Internet. Absorb this maxim and remember it, as it will save you on more than one occasion. Think about what information you do not want the whole world to know, including companies. You are free to publish whatever you want, but keep in mind that your data may not be safe.
In relation to what we were saying before, domains of companies such as Google, Facebook or Amazon have been attacked on several occasions. If this happens with large companies, imagine what could happen to your profile on social networks. While it is true that big hackers have no interest in private individuals, it is preferable to prevent unpleasantness. The easiest way to achieve this is to publish as little private data as possible. This is essential to avoid privacy mistakes, but you are the one who sets the bar between self-censorship and security.
Obsolete software
The vast majority of privacy errors go through this point. If you use obsolete software that is no longer supported or you simply do not update it, you are inviting attackers. Programs as basic as Mycrosoft Office are frequently patched precisely to prevent this. New attacks are discovered every day and companies adapt to them. That is why they are constantly providing updates. In fact, the most sophisticated attackers try to penetrate software security before they can release an update. Remember to keep automatic updates enabled in any case.
Cookies and autofill
Cookies are the main culprit for your browser to know you so well. Your name, your email, your phone number, your consumer preferences... Even if you have ever used your credit card to make an online purchase, the browser will remember its digits.
In this regard, most browsers offer the function of autocompleting the forms you have already filled out. This function, called autofill, autofill, saves the user time, but it can make one of the most glaring privacy mistakes. If anyone gets access to your browser, they can use autofill to enter any domain where you are registered. It is advisable, in short, to delete cookies periodically and not to abuse autofill.
Spam mail
The mail containing spam or malicious files not always end up in the spam folder. Some appear in our inbox and, if we open them thinking they are legitimate, we will be unpleasantly surprised. That is why we should check who is sending us the mail and from which address.
Most of the fraudulent emails imitate names of well-known companies such as banks or Internet giants. If you notice that the name is too long or that something doesn't add up, taking a look at Google will save you from falling into the trap. All you have to do is type the e-mail address in quotation marks and Google will search for exactly those words. If a website related to the company appears, then don't worry. If not, delete the email instantly. Finally, remember that due to security policies, no legitimate company will ask you for your username or password through email.
Unsecured free connection
Surely on more than one occasion you have found yourself in a hurry and without Internet connection. In those moments we accept any type of connection and, if the Wi-Fi network we are longing for appears, we connect without further ado. However, not all networks are secure. In fact, open networks available in bars or cafes are often not encrypted. This facilitates attacks MITM (Man In The Middle), which consist of blocking traffic and intercepting it in order to steal information.
It is advisable not to log in to your account and access it as a guest to avoid attacks. Obviously, the most advisable thing to do is to avoid the use of applications that include private data whenever we are connected to a public network. For example, no peeking into your bank account or your email on public Wi-Fi.
Typographical errors
It is very common for us to accidentally make typing mistakes. We live in an age where the pace of life is fast and we write without stopping to think. Therefore, on more than one occasion you may have filled out a form incorrectly. For example, when writing your email address, you included «@gmai.com», without the L. You don't care, you move on. You don't care, you go ahead and try again thinking that the email will not get anywhere. The fact is that it does arrive, and it is that there are companies that buy e-mail addresses taking into account these absent-mindedness. @homail, @gmlai, @htmal... All the variants you can imagine. They do it to deduce what your real email was and use this information to sell it to third parties or send spam to try to sell fraudulent products.
Websites without SSL certificates
If you enter a web page and a security warning pops up, be careful. It is very likely that the connection is not secure and does not have an SSL certificate. When this happens, the pages are more susceptible to attacks from third parties. It is well known that most users ignore these warnings, but we do not recommend it. Almost all companies that own trusted domains have certificates of this type. The key is to pay attention to the «not secure» note that appears in the browser to avoid certain pages.
These are just some of the privacy mistakes we make. There are many more, but the key is always the same: we must be careful about what we publish and check the platform on which we do it. By following these steps we will be one step ahead of the attackers.